
Introduction
Organizations in Iraq and the Kurdistan Region are accelerating digital transformation: modern data centers, cloud workloads, hybrid work, and complex OT/IT environments in oil and gas, telecom, banking, and government. At the same time, they face increasingly sophisticated cyber threats, from targeted ransomware and account takeover to insider misuse and supply‑chain attacks. Traditional, siloed security tools struggle to keep pace.
Palo Alto Networks Cortex XDR offers a modern approach built around extended detection and response (XDR), unifying endpoint, network, and identity telemetry in a single platform. This blog explores how Cortex XDR fits the regional context and what a practical adoption roadmap can look like for Iraqi and Kurdish organizations.
Why XDR Matters for Iraq and Kurdistan
1. Evolving Threat Landscape
- Critical industries such as oil and gas, logistics, telecom, and financial services in Iraq and the Kurdistan Region are highly attractive targets for regional and international threat actors.
- Many environments combine legacy systems with modern cloud services; attackers exploit this complexity to move laterally, bypassing traditional antivirus or perimeter‑only controls.
- Regulatory and contractual requirements from international partners increasingly expect strong incident detection, evidence‑based investigations, and clear reporting.
XDR directly addresses these issues by correlating events across multiple layers, giving security teams context instead of isolated alerts.
2. Skills and Resource Constraints
- Most organizations in the region have small security teams who must manage firewalls, endpoint protection, email security, and user awareness at the same time.
- Hiring and retaining senior SOC analysts is difficult; teams need technology that reduces noise, automates triage, and provides guided investigations.
Cortex XDR reduces alert fatigue through behavioral analytics and automated correlation, allowing limited teams to focus on true incidents rather than chasing every log entry.
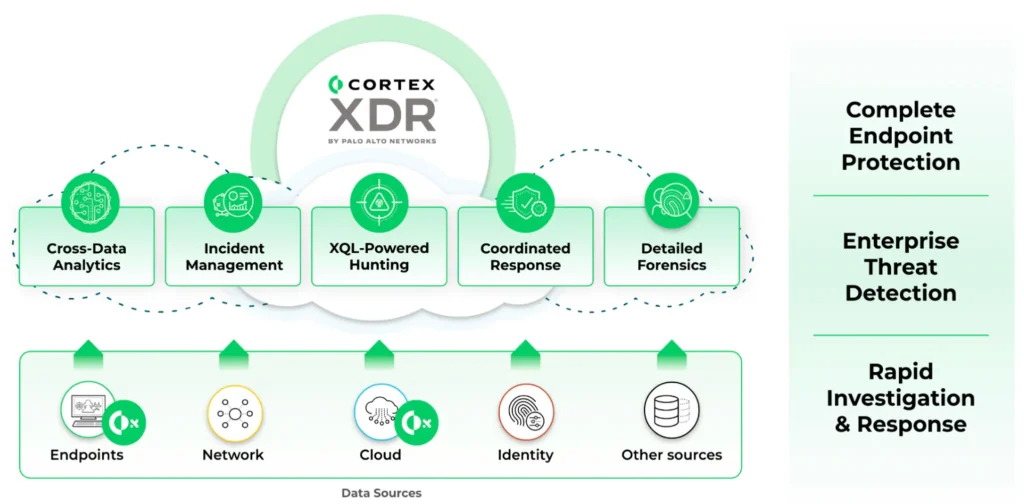
What Cortex XDR Brings to the Table
Unified Visibility Across Endpoints and Network
Cortex XDR ingests telemetry from:
- Endpoint agents (Windows, Linux, macOS servers and workstations)
- Palo Alto Networks next‑generation firewalls
- Cloud workloads and identity sources (depending on license and design)
By stitching these signals together, it builds a causality chain for each incident—showing where an attack started, how it spread, and which users or systems were affected. This is especially useful in environments with multiple branches such as Erbil, Sulaymaniyah, Duhok, Basra, and Baghdad, where full visibility is typically fragmented.
Advanced Prevention on the Endpoint
The Cortex XDR agent replaces or augments traditional antivirus and includes:
- Exploit prevention and behavior‑based ransomware protection
- Local machine‑learning detection to stop malware offline
- Host firewall and device control (USB, etc., depending on policy)
For organizations dealing with remote sites or harsh industrial conditions, this reduces reliance on constant connectivity to a central server.
Faster Investigation and Response
Key capabilities that matter for regional SOC teams include:
- Incident scoring and prioritization based on risk and blast radius
- Timeline views to reconstruct an attack within seconds, not hours
- Guided response actions (isolate endpoint, terminate process, block hash, etc.)
- Out‑of‑the‑box detection rules plus the ability to write custom analytics for local use cases (e.g., specific OT jump hosts or privileged accounts)
This can significantly reduce mean time to detect (MTTD) and mean time to respond (MTTR), which is crucial when an incident could impact operations in critical infrastructure or government environments.

Use Cases in Iraq and the Kurdistan Region
1. Oil & Gas and Energy
- Protect engineering workstations, jump servers, and business IT that interface with OT/SCADA networks.
- Detect abnormal user behavior such as unusual RDP connections from office networks into field sites.
- Provide forensic detail when international partners or auditors request evidence after a security incident.
2. Government and Public Sector
- Consolidate security monitoring for ministries, municipalities, and agencies that share a central data center.
- Use XDR analytics to identify account compromise in email and collaboration tools, and then trace lateral movement within the government network.
- Support national cyber‑resilience and CERT initiatives with structured incident data and reporting.
3. Banking and Financial Services
- Monitor endpoints used for core banking applications and internet banking support.
- Detect suspicious behavior involving SWIFT terminals or payment systems.
- Use strong incident timelines and evidence for regulatory reporting and communication with international correspondent banks.
4. Telco, ISP, and Service Providers
- Offer managed detection and response (MDR/XDR‑as‑a‑service) to enterprise customers across Iraq and the Kurdistan Region.
- Correlate endpoint and firewall data to detect botnets, credential stuffing, and DDoS preparation across the provider network.
Practical Deployment Approach
Phase 1 – Assessment and Design
- Map critical assets: domain controllers, file servers, ERP, OT gateways, and executive endpoints.
- Define initial scope (for example, 500–2,000 users) focusing on high‑risk systems and departments.
- Align with existing Palo Alto Networks infrastructure (if you already have PA‑Series firewalls or cloud security) to maximize visibility.
Phase 2 – Pilot and Baseline
- Deploy Cortex XDR agents to a controlled pilot group (IT, SOC, some business users).
- Integrate with at least one NGFW to enrich telemetry.
- Run in “learning” mode to establish a baseline and tune policies for false positives and local business behavior.
Phase 3 – Rollout and Integration
- Roll out agents to remaining endpoints in waves (by location or business unit).
- Integrate with ticketing systems (e.g., ServiceNow, Jira, OTRS) where possible to automate incident tracking.
- Define runbooks for common incident types: ransomware alert, suspicious PowerShell, risky macro, lateral movement, etc.
Phase 4 – Continuous Improvement
- Build local detection rules for region‑specific risks (for example, commonly abused remote‑access tools or regional malware families).
- Use periodic threat‑hunting sessions, leveraging the XDR data lake to look for dormant threats.
- Review metrics: reduction in incident volume, faster response, and fewer security outages affecting business operations.
Local Considerations for Iraq and Kurdistan
When deploying Cortex XDR in this region, organizations should consider:
- Bandwidth and connectivity: Some branch sites or fields may have limited links; deployment planning should account for update sizes and data upload volumes.
- Data residency & compliance: Clarify where XDR data is hosted and ensure it aligns with internal policies or local regulatory expectations.
- Language and training: Provide Kurdish and Arabic training materials for IT and security staff to ensure effective use of the platform.
- Partner ecosystem: Work with regional partners experienced in Palo Alto Networks deployments who understand local infrastructure and security culture.
Cortex XDR is well suited to the realities of Iraq and the Kurdistan Region: complex networks, critical infrastructure, limited SOC resources, and rising cyber risk. By consolidating detection and response across endpoints and networks, it helps organizations move from reactive firefighting to proactive, intelligence‑driven security operations.
With the right design, rollout, and local expertise, Cortex XDR can become a central pillar of cyber defense for enterprises and public institutions across the region.
If you share your target industry (oil & gas, banking, government, etc.), I can tailor a shorter version of this blog specifically for that vertical.
Here is the updated ending section you can append to your blog:
Get Started with MIROTECH
Get started with MIROTECH, the official partner and service provider of Palo Alto Networks in Iraq and the Kurdistan Region. Our team can help you assess your current security posture, design the right Cortex XDR architecture for your environment, and support you throughout deployment and daily operations.
Whether you are in oil and gas, government, banking, telecom, or enterprise, MIROTECH can provide local expertise, implementation services, and ongoing support to ensure you get the maximum value from Cortex XDR and the broader Palo Alto Networks ecosystem.






